These days WiFi networks are found everywhere: homes, offices, coffee shops, waiting rooms, and even airplanes. WiFi has become almost as ubiquitous as electricity; with the rise of the mobile internet, we find ourselves connecting to unfamiliar WiFi networks more and more often, and hackers have a new tool to take advantage of this — it’s called an “evil twin.”
An evil twin is an unsecured network with a strong signal in high traffic areas set up by hackers who know that passersby will connect. Any off the shelf router can be made into an evil twin if connected to a hacker’s laptop running the right software, or they can purchase a device specifically designed for this purpose online. These so-called “pineapples” are freely available online, can be small enough to fit in a pocket, and they start at only $99.99.
Once a device is connected to a wireless evil twin, it becomes the medium through which the device transfers data to and from the internet. Why is this dangerous? Imagine you’re sending letters back and forth with a friend, and someone who wants to steal your identity impersonates the postal worker who services your house. They continue to deliver the mail from your house to the post office and vice versa, so your conversation continues as normal and nothing seems amiss. However, they open your mail and read it before delivery, allowing them to monitor your correspondence. This is called a “man in the middle attack.”
Your WiFi router is like the postal worker who delivers information between your computer and the internet. Like the crooked postal worker, an evil twin can crack open the data sent by your computer and record it before passing it on. This allows the operator to access any data flowing between your device and the web. Many modern devices, such as phones, will automatically connect to nearby open networks, meaning they can fall into an evil twin without user input. And, due to automated features such as push notifications, your phone may be sending data back and forth through a network you don’t even realize you’re connected to. In addition, WiFi devices broadcast a list of the SSID’s (a WiFi network’s unique ID tag) of all the networks they’ve previously connected to, meaning a motivated hacker could find out what networks your phone has been connecting to, and by extension, where you’ve been.
It can all sound a little scary. Hackers can set up an evil twin cheaply and easily, and can pull in loads of people at a time, but they rely on the victims having poor knowledge of security risks. Keeping yourself safe from these kinds of attacks is as simple as picking up a few good security habits.
Don’t connect to unsecured networks unless you can verify the owner
WiFi networks can be named anything the owner wants, so “Starbucks WiFi” could be coming from that suspicious looking van in the parking lot. Don’t hesitate to ask your barista if they have WiFi when you pick up your latte and confirm that signal isn’t coming from an evil twin, but keep in mind that using even legitimate public WiFi networks can be risky.
Prevent your phone from automatically connecting to unsecured WiFi networks
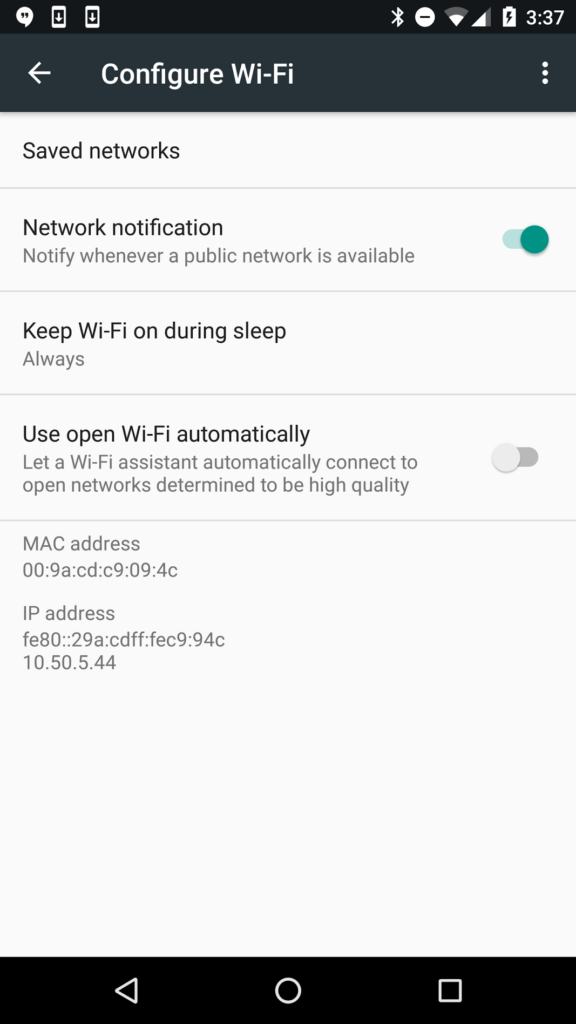
Many devices will automatically connect to the strongest nearby, unsecured WiFi signal. This means your phone could fall into an evil twin without you even noticing. If you’re on an iPhone, go into WiFi and scroll to the bottom, then turn on “Ask to Join Networks.” This will keep your phone from joining networks unless you explicitly give the ok. On Android, go into settings, and ‘forget’ open networks you’ve previously connected to, your phone will no longer connect to them automatically.
Be careful what information you’re sending over unsecured WiFi
If the network you’re connected to is an evil twin, all of this information will be flowing through the hacker’s hardware, which can leave it vulnerable to attack. You might be fine checking the news, but logging into your email or doing your online shopping should probably wait until you get home.
It can be overwhelming, trying to keep your data secure in an increasingly connected world. Hackers are devising new means of attack every day and at the same time more and more of our lives are online, but that doesn’t mean safety is impossible. Just the opposite in fact. Hackers often use these types of large dragnet approaches that rely on consumers’ ignorance to keep them vulnerable. When it comes to these kinds of attacks, staying safe is as simple as staying informed.


You must be logged in to post a comment.